SPAM
Types of Scam Emails
Phishing
Phishing emails are fraudulent email messages that appear to be sent by legitimate sources (a friend or another student, the University IT department, a bank, etc.) These messages usually include a link to click on that directs you to malicious website made to look like a login page or a webform designed to get you to enter private information (for example, your username and password.) The attackers then use the information the information they've collected from you to commit some form of malicious activity with your account or, worse, identity theft.
Most phishing emails attempt to trick recipients by threatening that they will lose something due to inaction. Examples of wording using in Phishing emails include:
- 'Your account will be deactivated if you don't CLICK HERE.'
- 'ACTION REQUIRED - MISSING FAFSA/Financial Aid Info. CLICK HERE for Document Review'
- 'A file has been shared with you. ONEDRIVE Document.'
- 'You have received a secure document from XXX. Click Here to access.'
- 'Unable to display full message. CLICK HERE to show full message.'
For additional information on Phishing, visit one of these online resources:
- https://www.phishing.org/what-is-phishing
- https://www.consumer.ftc.gov/articles/how-recognize-and-avoid-phishing-scams
Fake Part-Time Jobs & Fake Check Scams
Many universities have been affected by students and employees receiving emails from other student emails or outside addresses that indicate that their company/friend/mother/uncle/etc. is hiring for a part-time job.
- These 'jobs' range from pet or baby sitting to research or secret shopper jobs that students can do in their spare time to earn extra money.
- These are fake job scams that attempt to have individuals deposit a fake check.
- Students who reply and indicate interest receive responses asking to provide detailed contact information (address, date of birth, etc.)
- The scammers then indicate that you are 'hired' and send a fake check or money order to "cover start up wages/supplies."
- The check is often for $1,500-2,000, and the student is asked to keep some of the money as their payment and sent the larger remaining about of money from the check to someone else via gift card, wire transfer, or other means.
- A few weeks later, the initial check then does not clear and the individual who deposited the check is then out the money then sent on to someone else.
For more information on fake check scams, visit the following links:
- https://www.fraud.org/fake_check_scams
- https://www.ic3.gov/media/2017/170118.aspx
- https://www.bbb.org/pittsburgh/news-events/bbb-scam-alerts/2017/01/college-students-targeted-with-bogus-employment-offers/
Impersonation Emails & Gift Card Scams
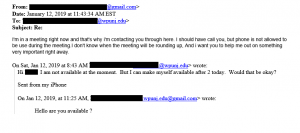
Impersonation emails are emails that seem be sent by a trusted colleague or friend and start with a simple question like 'Are you available?'
- These emails are sent so that they look like they are coming from the email of someone you know, but are actually sent from another email account used by a scammer.
- If you reply to the email, you'll be asked if you can do a favor for that person.
- Usually, the request is to purchase gift cards for some urgent need they have and then scratch of the redemption codes and email or text pictures to them.
- Once the scammer has the redemption codes for the gift cards, the funds are immediate moved to another account and your money is now stolen.
For additional information on impersonation emails and gift card scams, please visit the following links:
- https://www.chronicle.com/article/Phishing-Scheme-Targets/245535/
- https://www.zdnet.com/article/beware-phony-gift-card-email-scams-heres-why-attackers-love-using-them/
Sextortion Emails
Sextortion scams are scams in which you receive an email from a 'hacker' that indicates the person has had access to your accounts and computers for several months and will release embarrassing photos/videos/search history to your friends, family, or coworkers unless you pay them some form of ransom (usually requested in Bitcoin.) The emails may even include part of a password you currently or previously used.
These emails are rarely ever legitimate. In most cases, the emails are sent to individuals by the thousands using lists of emails - and possibly passwords - compiled from website hacks over the years. While the emails may be scary to read, our recommendation is always to just ignore and delete the email. It's possible that you may receive several iterations of the email, but all can safely be ignored.
For more information on sextortion email scams, visit the following resources:
- https://www.eff.org/deeplinks/2018/07/sextortion-scam-what-do-if-you-get-latest-phishing-spam-demanding-bitcoin
- https://www.cnbc.com/2019/06/17/email-sextortion-scams-on-the-rise-says-fbi.html
Reporting SPAM email
Students, faculty and staff can report SPAM messages to Microsoft for analysis. If you are ever unsure if an email message is legitimate or SPAM, please contact User Services by submitting a request online at https://www.wpunj.edu/helpdesk or by calling 973-720-4357.
Junk and Phishing
- Compose a new email
- Address the email to the Microsoft team that reviews messages as follows:
- For junk messages, address your email to junk@office365.microsoft.com
- Junk messages may contain disguised links that appear to be for familiar websites but in fact lead to phishing web sites or sites that are hosting malware.
- For phishing scam messages, address your email to phish@office365.microsoft.com
- Phishing is the attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
- For junk messages, address your email to junk@office365.microsoft.com
- Leave the body of the new message empty (remove any auto-populating signatures)
- Insert the junk or phishing scam message into your new blank email as an attachment. Note: Do not simply forward the junk or phishing message.
- Delete the original message
False Positives
Sometimes email messages are incorrectly identified as SPAM. To submit emails identified in this way:
- Compose a new email
- Address the email to not_junk@office365.microsoft.com
- Leave the body of the new message empty (remove any auto-populating signatures)
- Attach the email message that was incorrectly identified. Note: Do not simply forward the message.
- Delete the original message
Sources:
The State of Vermont, Department of Information and Innovation, "Instructions for reporting spam and phishing scam messages to Microsoft for Analysis